Overview
- Ongoing political tensions between Russia and Ukraine are at a breaking point, with the US and other NATO nations preparing to assist Ukraine if a military conflict arises.
- Russia and Ukraine have a long history of state-sponsored cyber conflicts, including both espionage and disruptive attacks.
- Recent cyber activity targeting Ukraine includes multiple government website defacements and WhisperGate, a wiper malware disguised as ransomware. IOCs for PolySwarm’s samples of WhisperGate are provided.
- Hacktivists recently attacked Belarus Railway to protest Russian troop transport and demand the release of “political prisoners.” This incident marked the first time hacktivists have leveraged ransomware in pursuit of political objectives.
- The cyber struggle between Russia and Ukraine has the potential to spill over and have a real-world kinetic impact. Our analysts provide a list of implications.

Figure 1 A map of Russia and Ukraine.
Ukraine became independent in 1991 following the collapse of the Soviet Union. The current power struggle between Russia and Ukraine began in 2014 following the Russian annexation of Crimea from Ukraine. Tensions continued to escalate and are now at what seems to be a breaking point.
At present, Russia opposes Ukrainian involvement with NATO, seeking to prevent NATO’s influence in the region. Regional analysts report it is unlikely NATO allies will expand their military influence in the region, which could further jeopardize their relationship with Russia. However, Ukraine has held joint military exercises with NATO forces in the past, and NATO countries have stated they are ready to step in and assist Ukraine if a Russian invasion occurs.
Russia reportedly has more than double the military manpower of Ukraine and has around 100,000 troops currently stationed along the Ukraine border. At present, the US reportedly has 8500 troops on standby to deploy to Eastern Europe, with nearly 3000 on the way; and NATO has sent ships and aircraft to the region. There have been reports of potential sanctions against Russia and imposing export controls for dual-use technology. Additionally, NATO countries may attempt to exclude Russia from the global SWIFT financial system, which could lead to a short-term inconvenience for Russia and a massive blowback to the US.
A spokesperson for Russian President Putin alleged the US is escalating tensions, and Putin reportedly accused the US of using Ukraine as a pawn against Russia without caring about Ukraine’s interests. A majority of the Russian people reportedly want peaceful relations with Ukraine. Meanwhile, the Biden administration accuses Putin of being the aggressor. At this time, Russia denies plans to invade Ukraine.
Past Cyber Operations
Russia and Ukraine have a history of state-sponsored cyber conflict. Russia was observed targeting Ukrainian systems in 2013 with Operation Armageddon, but the activity potentially began as early as 2005. In 2014, aligning with the Russian troop movement into Crimea, Ukraine’s fiber optic cables were tampered with. Websites were targeted with DDoS attacks, and the mobile phones of several Ukrainian politicians were hacked or jammed. This marked the beginning of Ukraine’s cyberwar with Russia.
In 2015 and again in 2016, Russia reportedly hacked Ukraine’s power grid. In 2017, Russian threat actors carried out a supply chain attack on Ukrainian assets using Petya malware. According to CrowdStrike, most of Russia’s cyber attacks targeting Ukraine have been linked to the state-sponsored threat actor dubbed Voodoo Bear. A recent post by Symantec profiled ongoing espionage operations against Ukraine by a Russian nexus threat actor group known as Shuckworm (Armageddon) and traced the activity back to the 2013 Operation Armageddon. PolySwarm has multiple Shuckworm campaign samples available. IOCs are listed at the end of this document.
Current Cyber Conflict
In mid-January 2022, over 70 Ukrainian government sites were defaced or disabled. The defacement message was written in Polish, Russian, and Ukrainian, with a political message crafted to create dissent among the ethnic groups. The Ukrainian Cyber Police and Ukrainian Security Service suspect the threat actors responsible for the defacements used multiple attack vectors, including leveraging the infamous Log4j vulnerability.
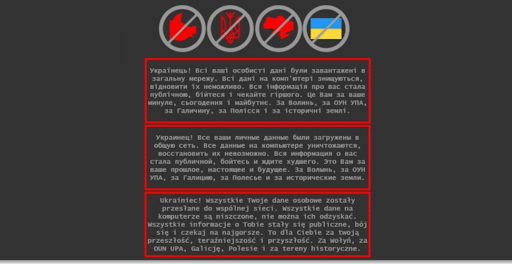
Credit: Herjavec Group
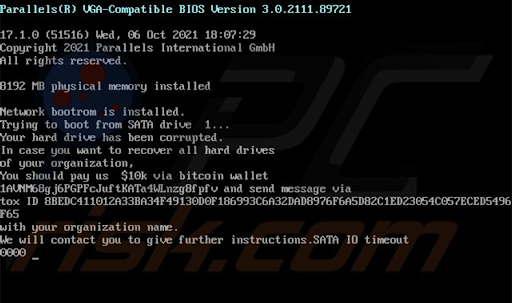
Additionally, the Ukrainian government, non-profit, and technology systems were targeted using a three-stage MBR wiper masquerading as ransomware and dubbed WhisperGate. The malware displayed a ransom note demanding payment to a Bitcoin address prior to wiping the master boot record. The Ukrainian government formally accused Russia of being behind the attacks. While no definitive attribution has been made, industry analysts note the possibility of threat actor involvement originating in Belarus, a close ally of Russia. Ukrainian officials suspect involvement by a Belarusian threat actor group known as Ghostwriter/UNC1151. PolySwarm has multiple WhisperGate samples available. IOCs are listed at the end of this document.
Hacktivist Activity
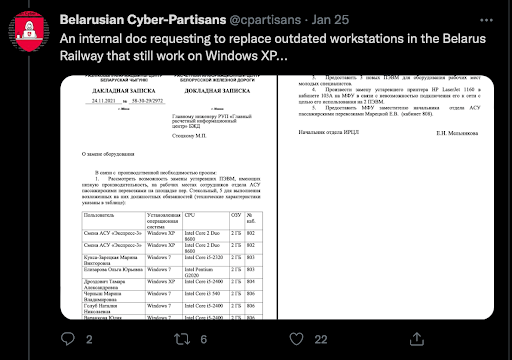
On January 24, the hacktivist group Belarusian Cyber Partisans claimed to attack Belarus Railway using ransomware. Their motivation was two-fold 1) to protest the railway’s plans to transport Russian troops and equipment that could be used to attack Ukraine and 2) to demand the release of 50 “political prisoners” in exchange for unlocking the railway’s systems. The group accessed the railway’s control systems, giving them the ability to shut down the railway’s signal systems, which could lead to collisions. However, Belarusian Cyber Partisans chose not to take such actions. The group tweeted what appears to be proof of the hack in the form of stolen documents. Emsisoft stated this incident appears to be the first time hacktivists have leveraged ransomware in pursuit of political objectives.
Both state-sponsored cyber operations carried out in support of kinetic warfare and hacktivist activity could have a wide range of real-world impact, including but not limited to:
- Supply chain attacks targeting military or civilian supplies
- Attacks on infrastructure, including power, water, and internet
- Attacks on transportation systems such as railroads to halt troop movement
- Attacks on government and military assets to cripple operations, create confusion or spread disinformation
- Attacks on weapons systems, aircraft, and other military equipment
IOCs
Shuckworm Campaign
33d30cc71324c24c74d7575d7bfaebd578607122cc581f093267a9c511da044b
119f9f69e6fa1f02c1940d1d222ecf67d739c7d240b5ac8d7ec862998fee064d
D8a01f69840c07ace6ae33e2f76e832c22d4513c07e252b6730b6de51c2e4385
Eef073bf432192d1cc0abb5afac8027f8a954b1fa1e8ca0c0b6cbeb31de54d35
6a64a8e2202db7f3a77d32b4852b71acf620f96580ca015e8bff8f5a09622032
85c14f4a7580623f967b9e9f7120a14bd3291f2177298e6bcb32e234af9bb2a8
3a4f3a39d32715a57c9985690a3fea76140ba832a1bfbb0c6aa3b6270661e12c
17b278045a8814170e06d7532e17b831bede8d968ee1a562ca2e9e9b9634c286
5271f59f0983382ac3e615265a904d044f8e3825c3d60b3d39a6e9a14bb3e780
WhisperGate
A196c6b8ffcb97ffb276d04f354696e2391311db3841ae16c8c9f56f36a38e92
Dcbbae5a1c61dbbbb7dcd6dc5dd1eb1169f5329958d38b58c3fd9384081c9b78
9ef7dbd3da51332a78eff19146d21c82957821e464e8133e9594a07d716d892d
34ca75a8c190f20b8a7596afeb255f2228cb2467bd210b2637965b61ac7ea907
Contact us at hivemind@polyswarm.io | Click here to subscribe to our reports.
