We recently completed the “New Engine Claiming and Management” milestone on our development roadmap. Our goal was to make it easier for Engine owners to build, configure and test an engine, and then join the PolySwarm Marketplace, so we’ve completely redesigned the architecture.
Why a New Engine Creation and Management Architecture?
Jun 16, 2021 11:57:47 AM / by Nick Davis posted in Explained, PolySwarm, Research
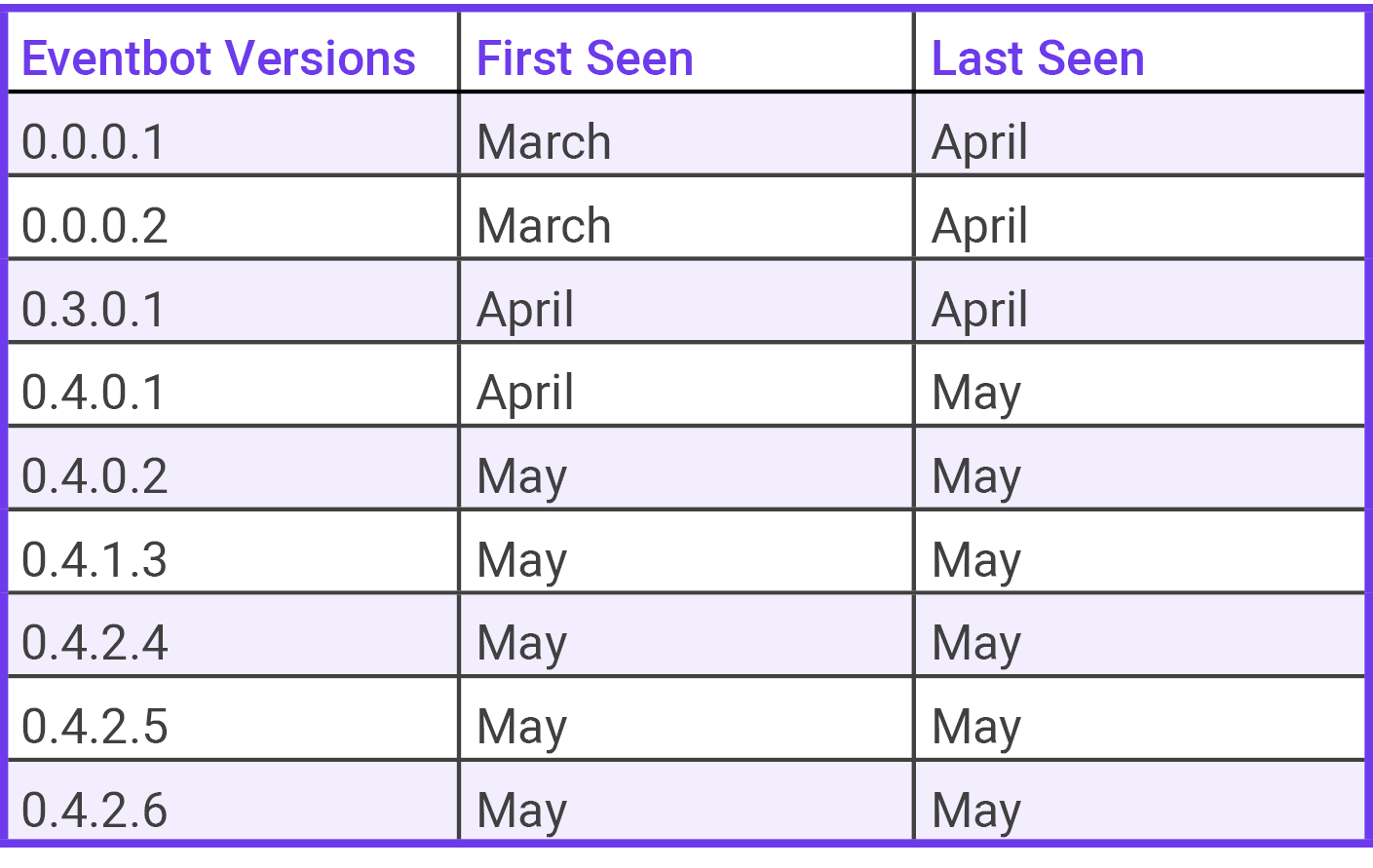
Initial Technical Analysis of EventBot Versions 0.4.0.2 - 0.4.2.6
May 20, 2020 4:30:09 PM / by Javier Botella posted in Research
Overview
PolySwarm’s threat research team has discovered new, previously unpublished versions of the EventBot malware family.
Join PolySwarm and Pacific Hackers Meetup for a digital event
Apr 14, 2020 5:30:51 PM / by PolySwarm Team posted in Interview, Speaking, Events, Research
We may not be able to connect in person right now, but we can still meet up...digitally of course! PolySwarm CTO Paul Makowski will be the featured guest of Pacific Hackers Meetup on Saturday, April 18, 2 p.m. PT - 4 p.m. PT. We're talking research-driven threat intel; the latest in malware detection techniques; PolySwarm's growing malware research community, polyX, and how you can get in on tha action; COVID-19 malware trends and more. So grab your computer, a beverage and spice up your Saturday with an interactive security discussion.
PolySwarm engine spotlight: researcher-driven engines detecting new and emergent malware
Mar 30, 2020 1:18:27 PM / by PolySwarm Tech Team posted in PolySwarm, Product, Research, Partner
To put it simply, there are some really cool threat detection technologies on the PolySwarm marketplace. As a recap, here at PolySwarm, we aggregate research-driven threat detection engines---both from AV companies and individual, specialized security experts---that compete in real-time to detect threats. Enterprises and individuals using PolySwarm benefit from deeper coverage of the malware landscape and unique threat intelligence from this aggregated network of engines.
Telegram users can now use PolySwarm’s free, malware detection bot
Mar 23, 2020 10:03:55 AM / by PolySwarm Team posted in Insider, Press, Media, Blockchain, Product, Research
The Telegram messaging app is used by over 200 million people around the world and has proven to be a great communication vehicle for individuals and companies. Unfortunately, Telegram is also an attractive target for bad actors looking to exploit the platform and people. From cryptocurrency stealers and miners, Telegram has seen its fair share of scams.
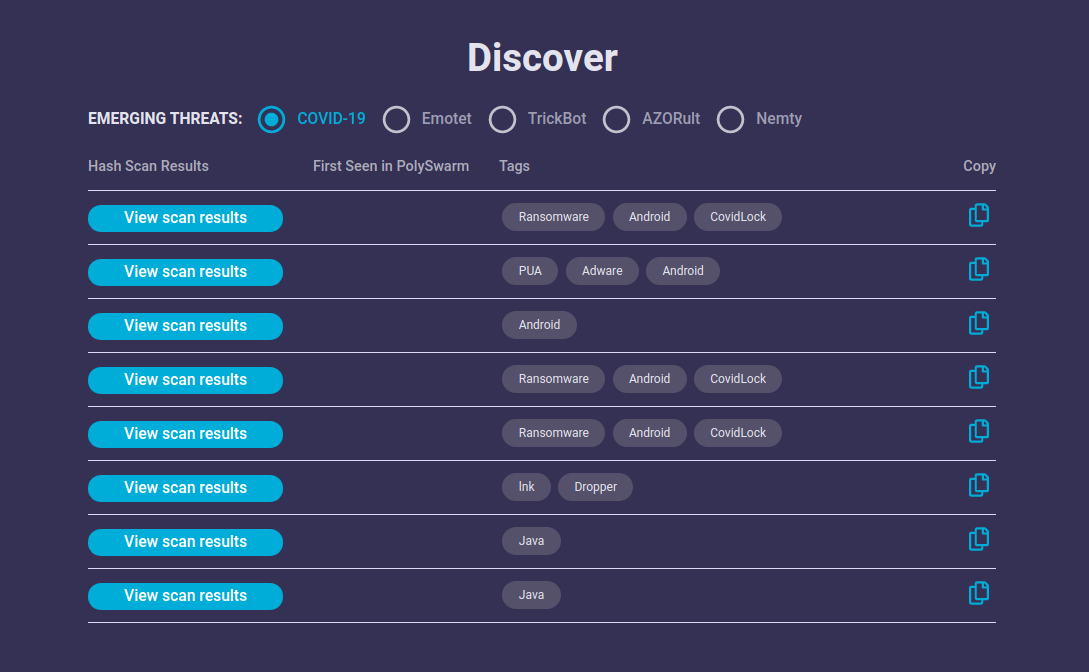
PolySwarm adds “Emerging Threats” feed, includes stream for COVID-19 malware samples
Mar 19, 2020 2:10:55 PM / by PolySwarm Team posted in Research
The world is experiencing a trying time, and every sector is impacted in some way by the COVID-19 pandemic. The unfortunate reality is that in times of crisis, hackers exploit vulnerabilities in systems...and humans: the COVID-19 pandemic is no exception. Over the last two weeks, here at PolySwarm, our malware analysts have seen a severe increase in pandemic related cyber threats--from Android ransomware to malware-laden “coronavirus map trackers”--that prey on people’s fragility and trust.
Latest samples of ZeroCleare, Iranian state-sponsored malware, available on PolySwarm
Jan 9, 2020 2:09:01 PM / by PolySwarm Tech Team posted in Insider, Explained, PolySwarm, Threat Hunting, Research
Today, PolySwarm, a threat intelligence platform used to detect new and emerging malware, releases information about a new variant of ZeroCleare (a destructive malware attributed to Iran). PolySwarm Community (free) and Enterprise users were able access to the full content of this sample before it appeared on VirusTotal.
Emotet's Christmas-themed phishing email ramps up - get hashes and file details in PolySwarm
Dec 18, 2019 2:04:51 PM / by PolySwarm Team posted in Research
Cybercriminals behind Emotet, one of the most prolific botnets in recent history, have ramped up a new Christmas-themed phishing attack. It lures victims to download malicious attachments related to "menus" for an upcoming Christmas party.