NectarNet - NCT Token Rewards for Cyber Security Data
Jan 31, 2022 8:56:00 AM / by PolySwarm Team posted in Insider, Explained, Product
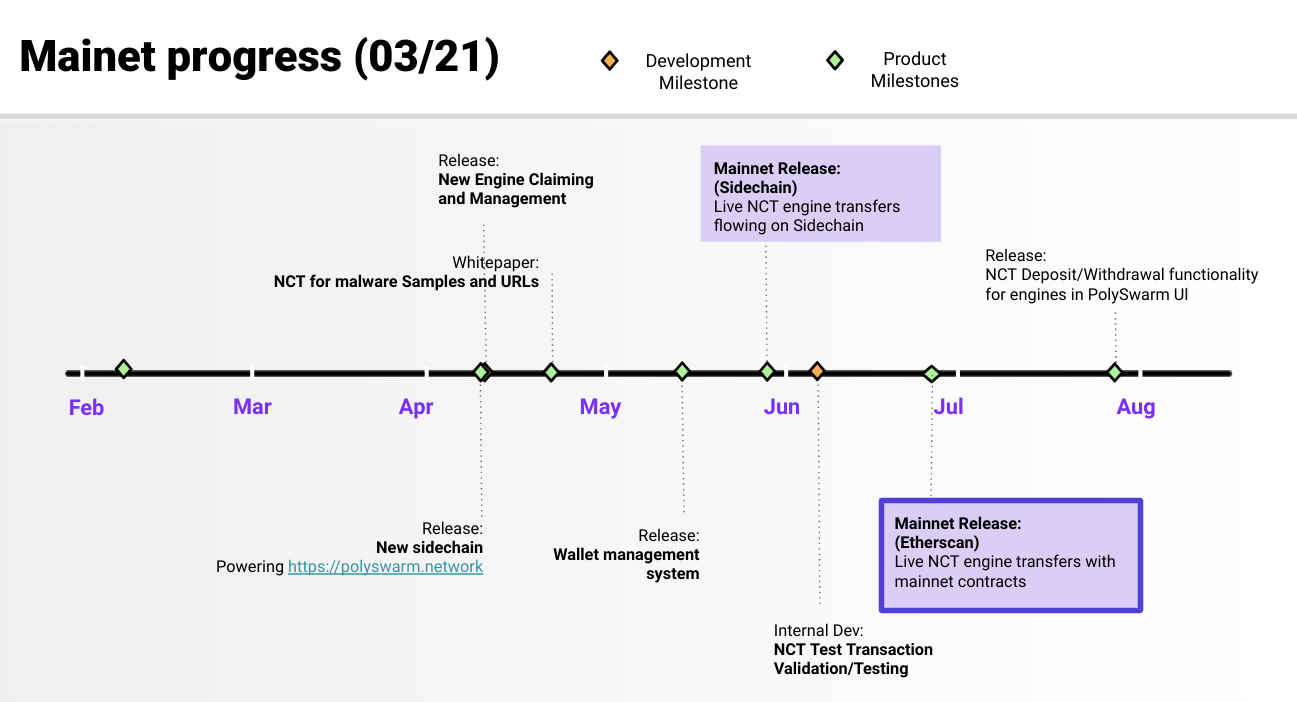
Progress to date and key milestones ahead
Mar 26, 2021 2:56:41 PM / by PolySwarm Team posted in PolySwarm, Product
The last 12 months have been intense yet very productive for PolySwarm, as we have scaled our platform, fast-tracked user acquisition and released new key features.
Let’s do a quick recap of what we’ve accomplished before we get into what lies ahead of us.
PolyScore™, the most advanced threat-scoring algorithm for malware
May 18, 2020 3:27:03 PM / by PolySwarm Team posted in Product
PolySwarm announced today the release of PolyScore™, a threat scoring algorithm that provides the probability that a given file contains malware in a single, authoritative number.
TeamT5's ThreatVision APT detection engine joins PolySwarm's marketplace
May 6, 2020 2:11:30 PM / by PolySwarm Team posted in Product, Partner
"We are excited to join PolySwarm, and to contribute to the network with our specialized APT intelligence in the Asia Pacific region" says TeamT5 CEO, TT Tsai. "We as a team, will bring the experience of our clients to the next level.
PolySwarm now integrated with leading SOAR platform ThreatConnect
Apr 13, 2020 1:30:04 PM / by PolySwarm Team posted in PolySwarm, Product, Partner
Enterprises, OEMs, MSSPs can now access PolySwarm's novel file reputation and threat detection services via leading SOAR platform ThreatConnect, Inc.
ThreatConnect users can access PolySwarm--a crowdsourced threat detection tool, that enables better detection against new and emerging malware--for file reputation and threat intelligence. Cyber analysts using ThreatConnect's Security Operations Platform can download and operate the solution from a single pane of glass.
PolySwarm engine spotlight: researcher-driven engines detecting new and emergent malware
Mar 30, 2020 1:18:27 PM / by PolySwarm Tech Team posted in PolySwarm, Product, Research, Partner
To put it simply, there are some really cool threat detection technologies on the PolySwarm marketplace. As a recap, here at PolySwarm, we aggregate research-driven threat detection engines---both from AV companies and individual, specialized security experts---that compete in real-time to detect threats. Enterprises and individuals using PolySwarm benefit from deeper coverage of the malware landscape and unique threat intelligence from this aggregated network of engines.
Telegram users can now use PolySwarm’s free, malware detection bot
Mar 23, 2020 10:03:55 AM / by PolySwarm Team posted in Insider, Press, Media, Blockchain, Product, Research
The Telegram messaging app is used by over 200 million people around the world and has proven to be a great communication vehicle for individuals and companies. Unfortunately, Telegram is also an attractive target for bad actors looking to exploit the platform and people. From cryptocurrency stealers and miners, Telegram has seen its fair share of scams.
PolySwarm provides latest enhancement to Basis Technology's incident response solution, Cyber Triage™
Mar 16, 2020 11:19:35 AM / by PolySwarm Team posted in Press, Media, Product
Today we are pleased to announce that Basis Technology has become a PolySwarm customer. Basis Technology’s incident response software, Cyber Triage™, plays an important role in the fight against cybercrime; PolySwarm will now help enhance this critical technology.