Dark Theme in PolySwarm UI has arrived
Sep 24, 2019 2:31:35 PM / by PolySwarm Team posted in PolySwarm, Product
Introducing Virusdie, a powerhouse URL scanner on PolySwarm
Sep 17, 2019 2:03:17 PM / by PolySwarm Team posted in PolySwarm, Product, Partner
Get better threat intelligence with Metadata Searching in PolySwarm
Sep 10, 2019 12:07:38 PM / by PolySwarm Team posted in Explained, PolySwarm, Product
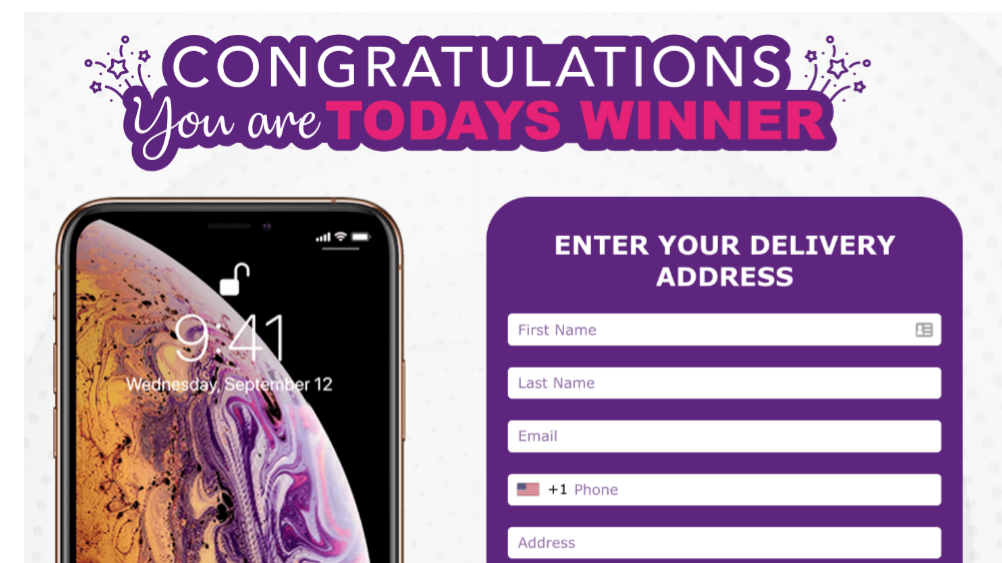
Latest phishing scam uses sneaky Google Calendar invite to bait potential victims with promise of iPhone
Sep 5, 2019 12:04:38 PM / by PolySwarm Team posted in Explained, PolySwarm, Product, Research
Do you ever see a mysterious calendar invite appear on your Google Calendar? If the answer is yes, there’s a good chance you are the victim of a calendar invite phishing scam.
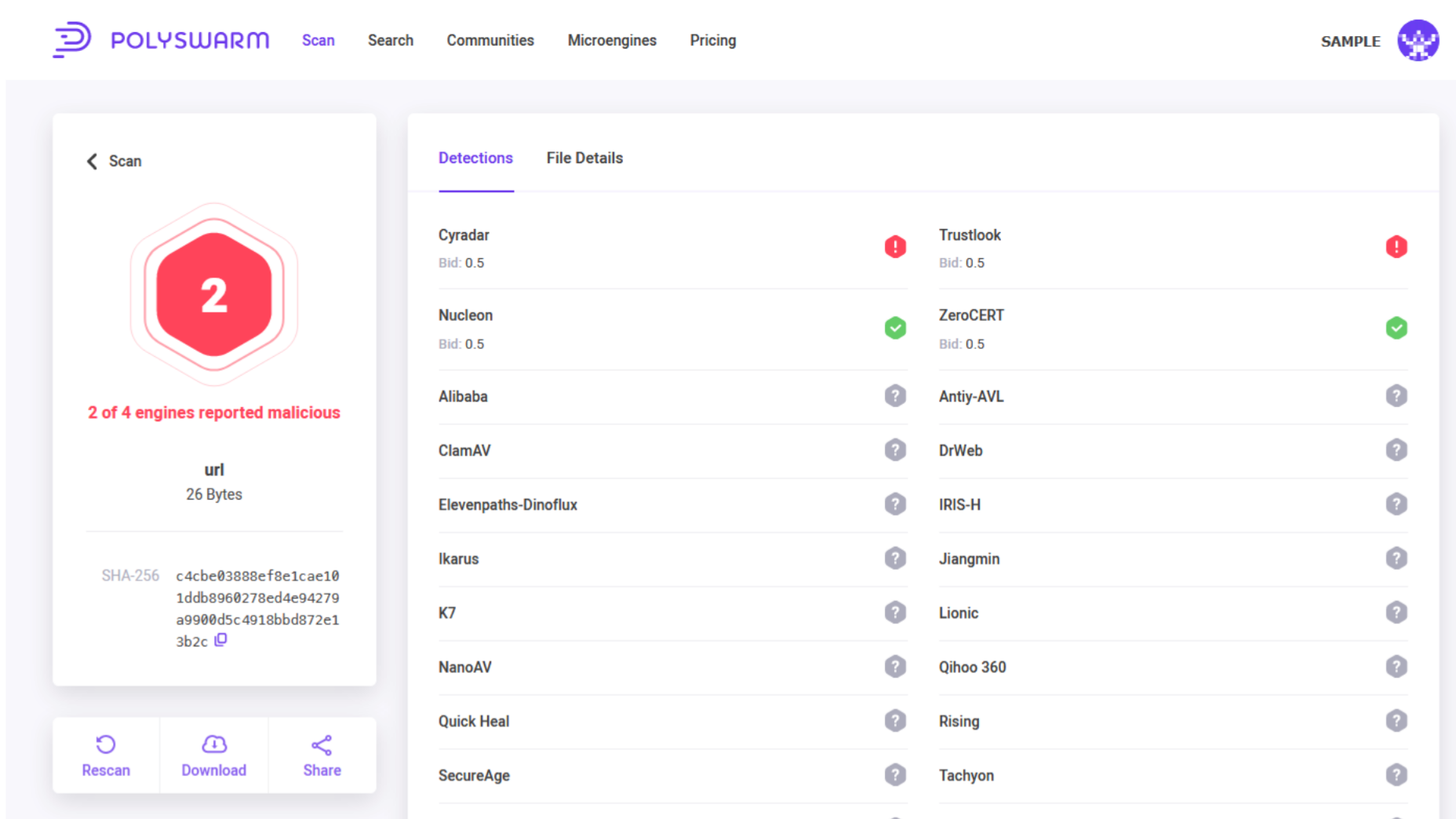
URL Scanning now available in PolySwarm
Aug 29, 2019 1:07:20 PM / by PolySwarm Team posted in Explained, PolySwarm, Product, Threat Bounty
The PolySwarm marketplace launched earlier this year, giving users the ability to gain intelligence on files from a competitive network of crowdsourced scanning engines from around the world. Now, PolySwarm users also have access to real-time information on suspect URLs, domains, and IPs.
Using PolySwarm Threat Hunting and Metadata Searching for intel on 0-days
Jul 29, 2019 8:29:00 PM / by Katherine Yan and Javier Botella Fernandez posted in PolySwarm, Product, Threat Hunting
A deep dive into using PolySwarm’s hunting features to identify malware. This demonstration shows how Threat Hunting and Metadata Searching helps analysts gather info on 0-day malware using EvilGnome as an example.
Introducing the first ever 'threat bounty'
Jun 30, 2019 10:13:00 PM / by Anna Keeve posted in Explained, PolySwarm, Product
PolySwarm’s threat detection marketplace has created the possibility of a new type of cyber-related bounty: say hello to the threat bounty